On the 3rd January 2019 Yaacov Apelbaum posted an in depth analysis of access to the DNC mail server
So who Pwned the DNC’s and Podesta’s emails? The Russians? Romanians? Or was it just your run of the mill developer/sysAdmin/staffer with an axe to grind? To find out more, check out the post by William Binney and Larry Johnson. Here is a little illustration that helps focus some of their data transfer rate arguments and expand on other cyber security points:
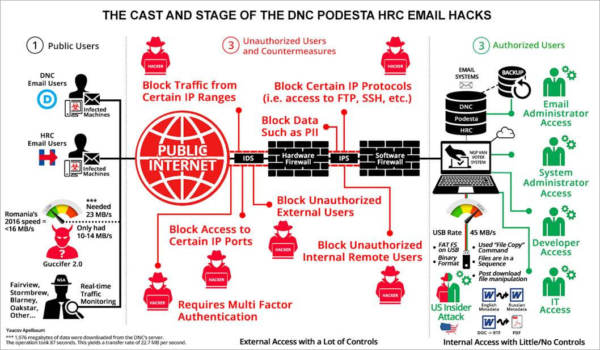
If you are still confused about the who, what, when, where, and how, you are not alone. The reason for this heavy fog is that it’s impossible to separate the spin from facts without access to the forensic data–which for some reason doesn’t’ seem to make itself available. As far as the pro and con arguments for a local vs. remote access are concerned, yes, theoretically an external attacker could have used a cocktail of zero day + remote privilege elevation + password recovery against the cloud based NGP VAN voter system, but so could a local user/administrator at a fraction of the time and effort.
What about the identity of the perp? According to the WaPo (using Crowdstrike, the DOJ, and their other usual hush-hush government leaker in the know), the attack was perpetrated by a Russian unit lead by Lieutenant Captain Nikolay Kozachek who allegedly crafted a malware called X-Agent and used it to get into the network and install keystroke loggers on several PCs.
…
End conclusion
In lieu of answering these pesky questions, we are left with the only remaining explanation that uses the following formula for predicting cyber attack origins:
“Path of Least Resistance”+
“Principle of Least Effort” +
“Opportunity” +
“Motive”
= “Insider”,
AKA one of them green guys on the right side of Image 1.
Read whole analysis and and commentary in Yaacov Apelbaum’s Blog